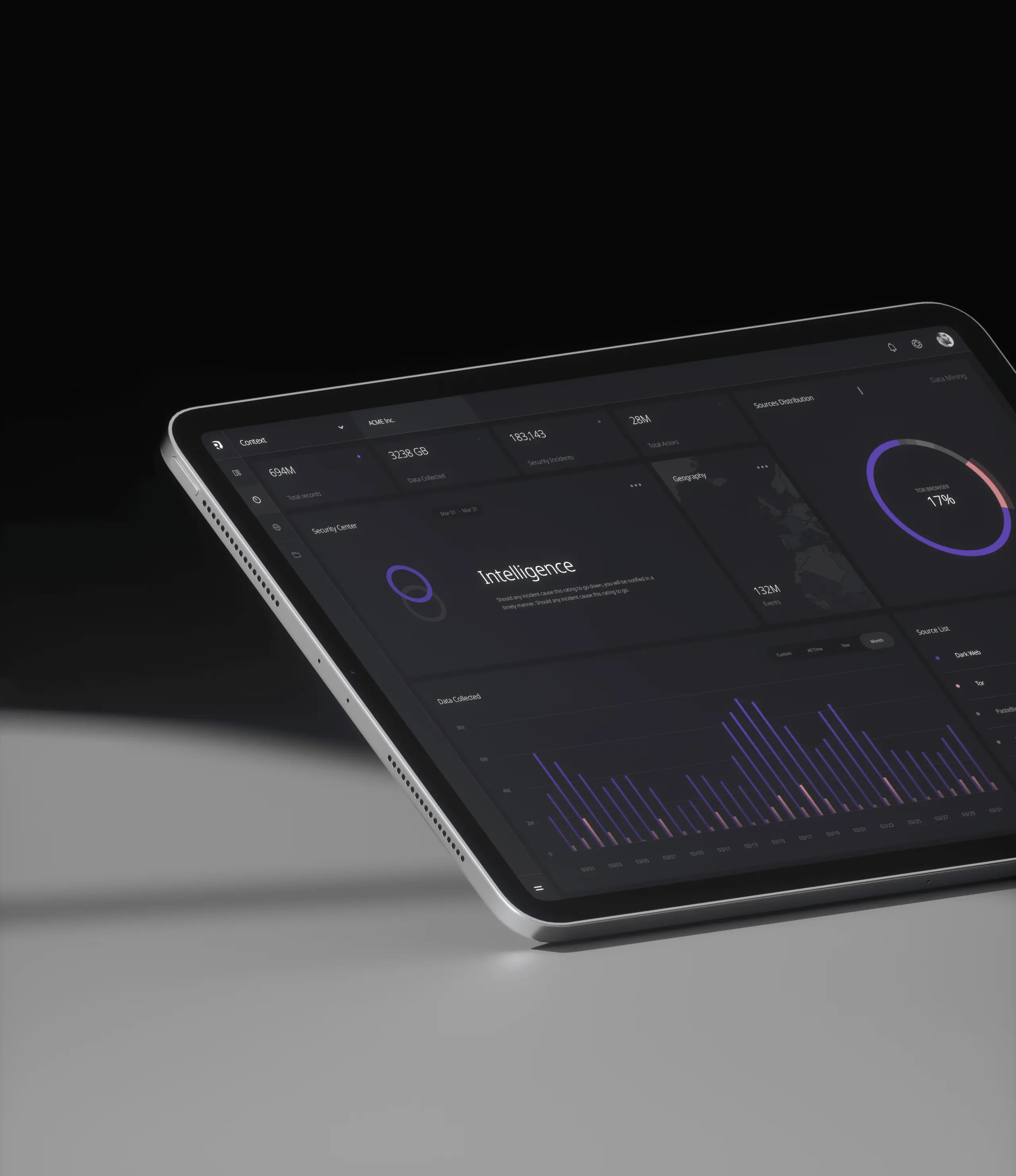
Cyber Threat Intelligence Platform
Context™ is an Cyber Threat Intelligence Platform from Resecurity™ for enterprises and governments to accelerate threat analysis.
01
Identifying the exposure of sensitive data & confidential documents.
02
Continuously updating repository of underground communities & marketplaces.
03
Lightning-fast search reaching the darkest corners of the Internet.
04
Delivering global visibility across all continents.
Context™
Cyber Threat Intelligence
With the emergence of new threats and security challenges on a daily basis, it’s now more than ever important to use effective tools to achieve a timely in-depth analysis of any digital threat.
Context TM is an intelligence platform to accelerate analysis, prevention, and investigation workflows. Lightning-fast search and data science serve analysts, investigators, SOC/DFIR teams, Risk management, and C-level security executives
Capabilities Of Cyber Security Intelligence Platform:
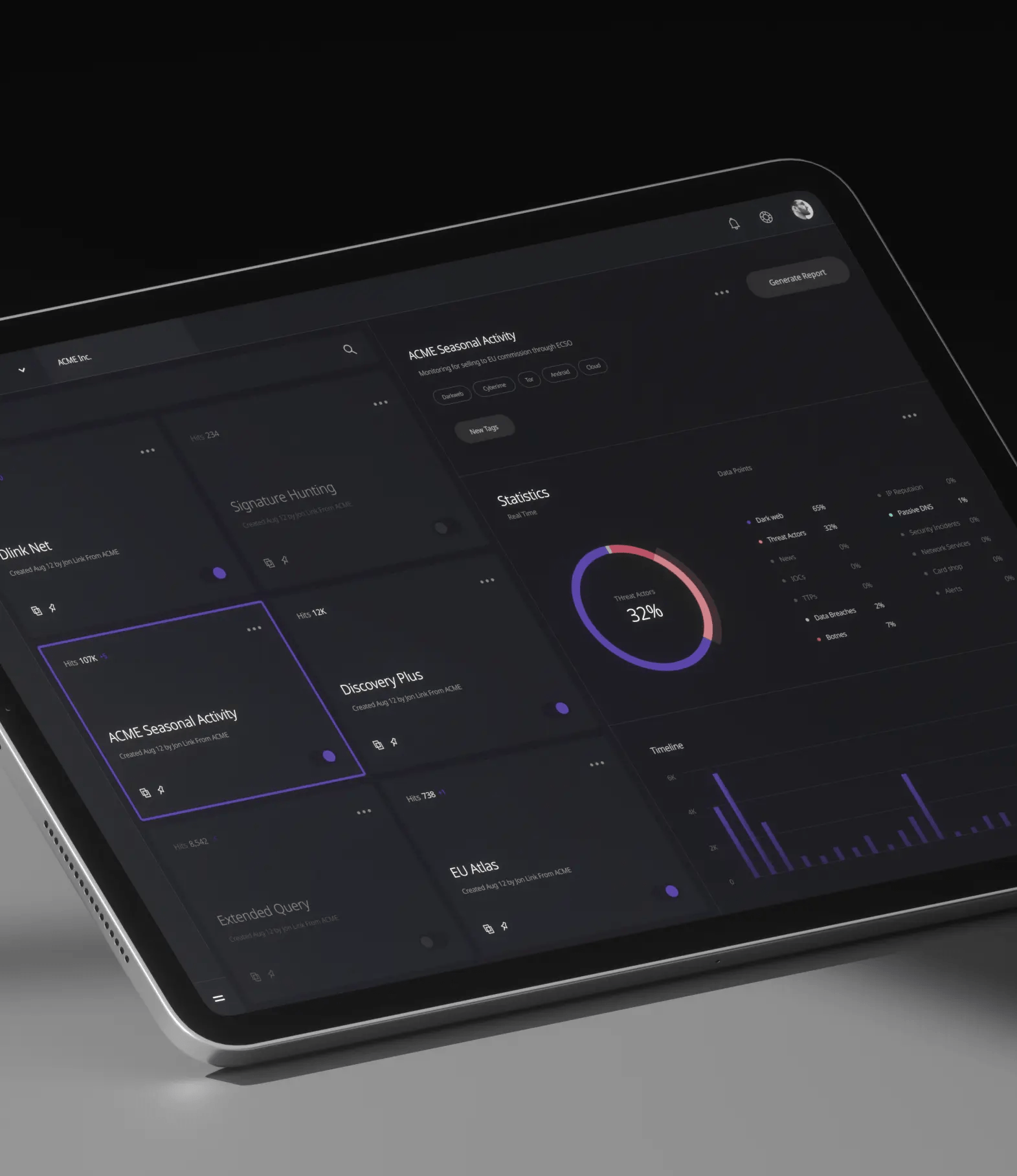
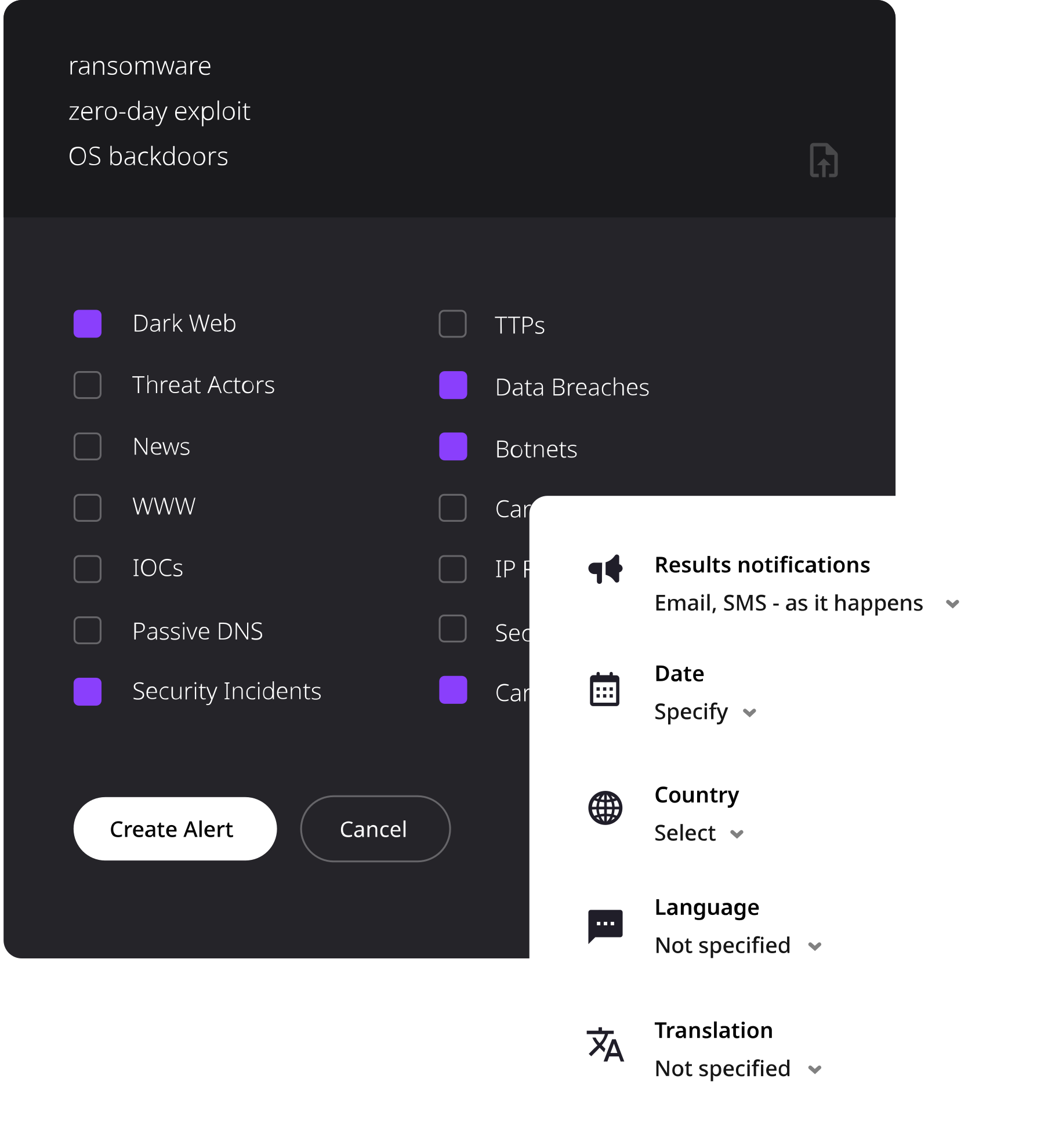
Actionable Big Data
Feel the difference of ContextTM, the ability to draw from an unparalleled number of sources gives ContextTM the leading edge in Cyber Security.
- Botnet
- Darkweb
- Threat Actors
- ISP Traffic
- Data Breaches
- Credit Cards
- Malware
Investigate Threat Actors
Context™ is based on a classic six-step process called the Intelligence Cycle. Used by government agencies and industry experts to support a balanced and comprehensive approach to intelligence gathering and analysis
INTELLIGENCE CYCLE
The Six-Step Process
01
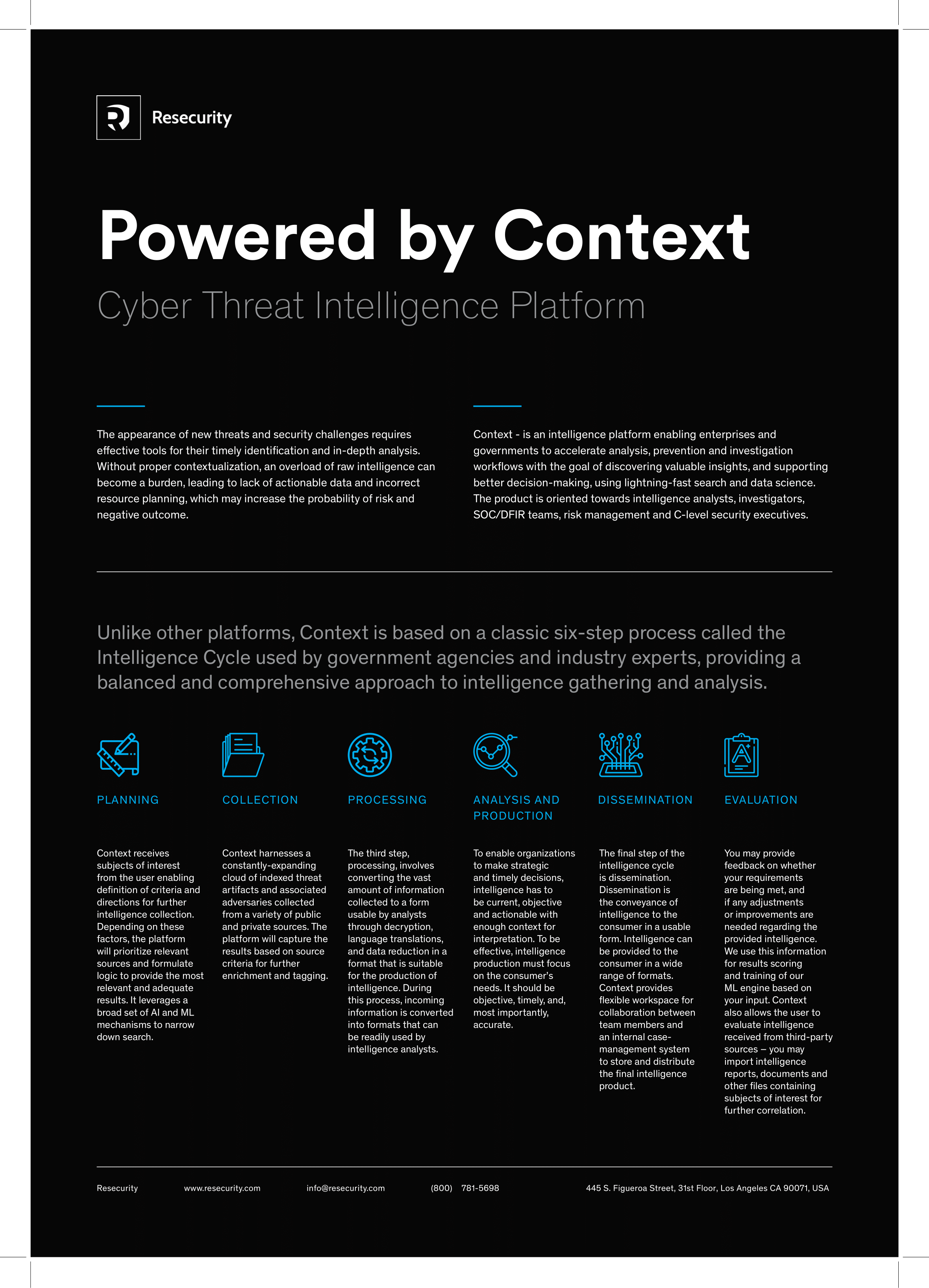
PLANNING
ContextTM receives subjects of interest from the user enabling a definition of criteria and direction for further intelligence collection. Based on specific factors, Context™ prioritizes sources by leveraging AI & ML mechanisms to formulate the most adequate results
02
COLLECTION
ContextTM harnesses a constantly expanding cloud of indexed threat artifacts and associated adversaries. The platform captures the results based on source criteria for further enrichment and tagging.
03
PROCESSING
This involves converting vast amounts of information collected to form usable data through decryption, language translation, and data reduction forming a suitable structure for intelligence production.
04
ANNALYSIS AND PRODUCTION
For organizations to make strategic and timely decisions, intelligence must be current and actionable with enough context to fully interpret. Effective intelligence production focuses on the consumer’s requirements
05
DISSEMINATION
To convey the intelligence to the consumer in a usable form, intelligence can be provided to the consumer in a variety of formats. ContextTM is flexible, providing a workspace for collaboration between team members to store and distribute the final intelligence dossier.
06
EVALUATION
Providing feedback on whether your requirements are met is fundamental to creating a successful intelligence dossier. Adjustments or improvements to the intelligence can be made to suit your requirements. This information is used to score and train the ML engine.
ContextTM Draws On Data Comprising
5B+
Threat artifacts, including indicators of compromise (IOCs), indicators of attacks (IOAs), tools, tactics and procedures (TTPs) of adversaries with valuable meta-data stored in a historical form used to deep-dive investigations.
9M
Profiles of threat actors collected from various underground communities and criminal marketplaces, intelligence reports and security expert communities with associated metadata.
300M+
Fully indexed and translated Dark Web data entries with extracted artifacts, graphical screenshots and link visualizations.
40
LANGUAGES
A built-in offline translation solution and unique linguistic expertise provide details on threat actors’ digital chatter.
20K+
SOURCES
A continuously updated repository of Dark Web sources, including Tor; I2P, Freenet, IRC, IM groups (Telegram) and more.
Team
Our team is ready to act as and when your organization requires a specific skill set from any one of a vast array of cyber security vertices. Our team is trained in multiple specializations, we are here to help you and your organization so business remains unaffected.
Download Datasheet
Cyber Threat Intelligence Platform Powered by Context™
Unlike other platforms, Context is based on a classic six-step process called the Intelligence Cycle used by government agencies and industry experts, providing a balanced and comprehensive approach to intelligence gathering and analysis.
Product Demo
Cybersecurity Solutions and Services
Try Resecurity™ Cyber Threat Intelligence Platform.
Schedule a demo now with Bulwark Technologies and experience the full capabilities of Resecurity™ Cyber Threat Intelligence Platform powered by Context™
Schedule a FREE Demo
"*" indicates required fields
