The Unsolved Problem
Your security stack is more vulnerable than you think
For years, companies have relied on stacking more security tools and building taller barriers, hoping to prevent breaches. Yet, despite these efforts, security incidents and downtime keep increasing. Perhaps the real challenge isn’t building stronger walls, but rethinking our approach to protection.
Average number managed by mature organizations
Annual cost of downtime for Global 2000 companies.
Average cost of a single ransomware or extortion attack.
Fail to maintain policy compliance.
Result from unpatched vulnerabilities.

Resilience Across Every Layer of Your Security Stack
Device Firmware : Ensure the core system of every device is secure and tamper-resistant.
Operating System & Applications : Keep OS and business-critical apps protected from threats and corruption.
Data Security : Safeguard sensitive information wherever it resides, whether on devices or in the cloud.
Application Security : Detect and prevent vulnerabilities within the software you rely on.
User Security : Protect employees with authentication, identity management, and access controls.
Endpoint Security : Maintain strong defenses on laptops, desktops, and mobile devices.
Network Security : Monitor and secure traffic across wired and wireless networks.
Perimeter Security : Strengthen defenses at the edge, controlling access to your organization’s resources.
The only purpose-built solution for true enterprise cyber resilience
Continuously enforced cybersecurity foundation
Maintain unbreakable security through automated patching and remediation across operating systems and applications — closing gaps before they can be exploited, ensuring configurations remain aligned with enterprise requirements, and scaling through flexible workflows to reduce risk and eliminate manual effort without added complexity across enterprises.

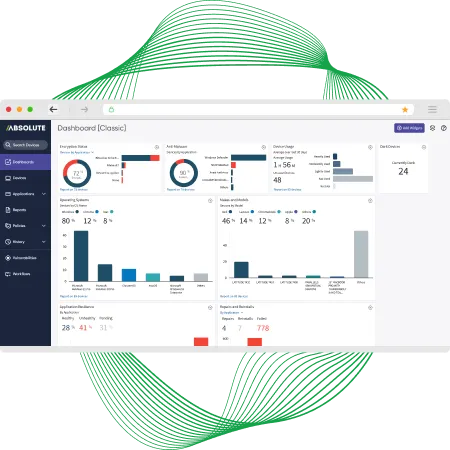
Always-on security and management controls
Keep critical security and IT management controls always operational, with continuous status monitoring of more than 80 tools and automatic restoration when they’re missing, disabled, or degraded — ensuring controls remain fully active, optimized, and compliant, so protection doesn’t silently fail due to misconfiguration, system drift, or active attacks.

Secure, resilient access — wherever work happens
Get secure, zero-trust access to web, cloud, and private applications, ensuring users connect safely wherever they are, while dynamic policy enforcement and threat prevention at the point of connection protect sensitive data, preserve a consistent, user-friendly experience, and keep access reliable, scalable, and resilient as environments change.
Immediate recovery designed for continuity
Ensure rapid recovery to a trusted state, with remote restoration of compromised devices to a compliant, known-good condition in minutes — not hours — supporting both reactive response and proactive restoration so devices can be returned to a trusted, compliant state on demand, maintain operational integrity, and ensure business continuity.
What sets Absolute Security apart
At the core of modern cyber resilience is a security foundation that strengthens every layer of your technology environment. By integrating firmware-level visibility, continuous endpoint protection, and real-time intelligence, Absolute establishes a resilient security framework designed to remain active, even when threats attempt to disable it.
This foundation acts as a self-reinforcing backbone for your organization, supporting business continuity, rapid ransomware recovery, and faster incident response. It enables zero trust principles to move beyond theory and become part of everyday operations, minimizing downtime and reinforcing overall organizational stability.
Persistence
Our undeletable connection is embedded in the firmware of over 600 million devices from close to 30 international system manufacturers. It can't be removed or tampered with, giving you a permanent line of sight and control.
Resilience
We create an unbreakable, self-healing link between your devices and our platform. If a critical security control is disabled or corrupted, we automatically restore it to its intended state.
Intelligence
Our platform processes over 3.1 billion API calls from endpoints daily, providing unique, actionable data that strengthens your entire security stack and informs a more resilient strategy.
Why leaders choose Absolute Security
Enterprise leaders rely on Absolute Security because it delivers resilience you can trust, insights you can act on, and operational continuity you can count on even in the face of breaches, ransomware, or unexpected disruptions.
- Trusted by CIOs and CISOs at the world’s most resilient organizations.
- Ensures business continuity during ransomware attacks, breaches, and unexpected disruptions.
- Strengthens security posture and maintains compliance across complex environments.
- Backed by patented technology and proven endpoint resilience.
Product Demo
Book your personalized demo of Absolute with Bulwark
Shift from outdated protection to a platform that builds resilience from the inside out— with firmware-embedded security, self-healing control, and endpoint resilience.
What can you expect:
- A brief conversation to assess what Absolute can do to protect your network and devices
- Live product demo with insight into how to get the most out of your partnership with Absolute
- Discuss your specific use case and goals to determine the best path forward for your business
Schedule a FREE Demo
"*" indicates required fields
