Keystrike
STOP USER IMPERSONATION & LATERAL MOVEMENT
ATTACKS WILL HAPPEN, BUT CONSEQUENCES ARE OPTIONAL
Keystrike is a cybersecurity company focused on redefining trust at the human–machine interface. We protect critical systems by verifying that every keystroke and mouse action originates from a trusted, physical device, ensuring commands executed on servers truly come from authorized users, not malware or compromised users. Our technology adds a powerful security layer beyond passwords and MFA, preventing lateral movement, user impersonation, and unauthorized access across IT and OT environments.
Keystrike integrates seamlessly with SSH, RDP, and other protocols, without disrupting operations. We work with organizations operating critical infrastructure and high-risk environments, delivering real-time assurance, reliable protection, and a stronger foundation for modern zero trust security.
Bulwark Technologies is an authorised distributor for Keystrike.
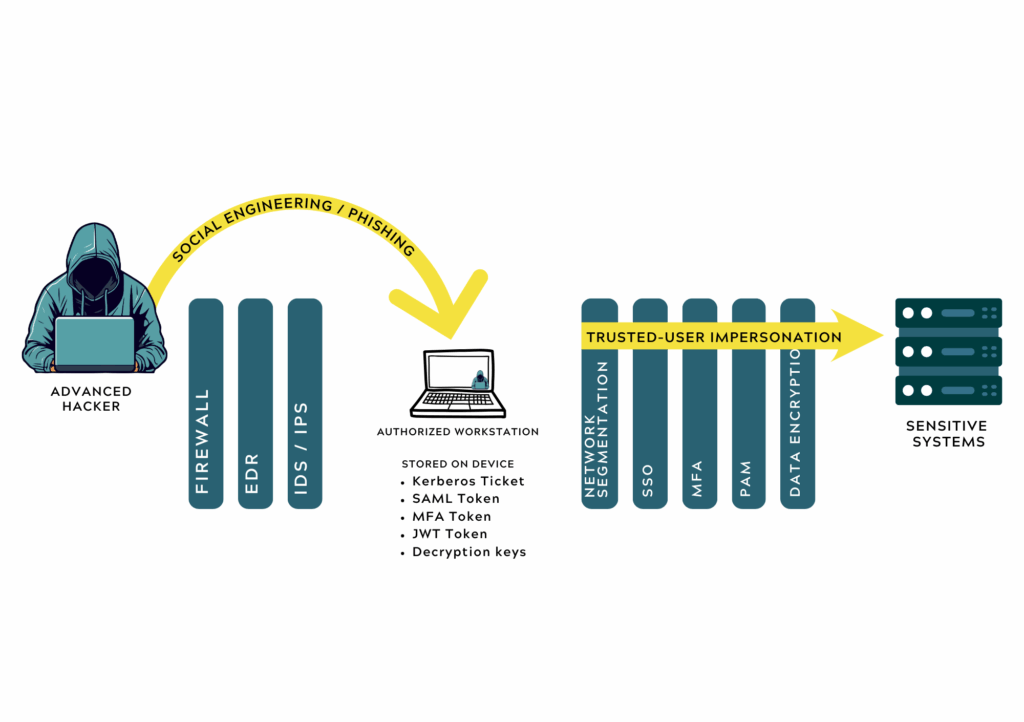
The problem: PAMs. MFAs, EDRs, XDRs, Firewalls, policies, network segmentations etc. are not enough to protect our systems.
Advanced hackers don’t try noisy attacks but rather aim for the weakest links, the people, with phishing campaigns and social engineering. Once a person falls for the attack, then the attacker has full access to the compromised device. Now, since the authenticated user has logged into the sensitive systems, then the hacker has the same access, through user impersonation.
The Solution - Keystrike
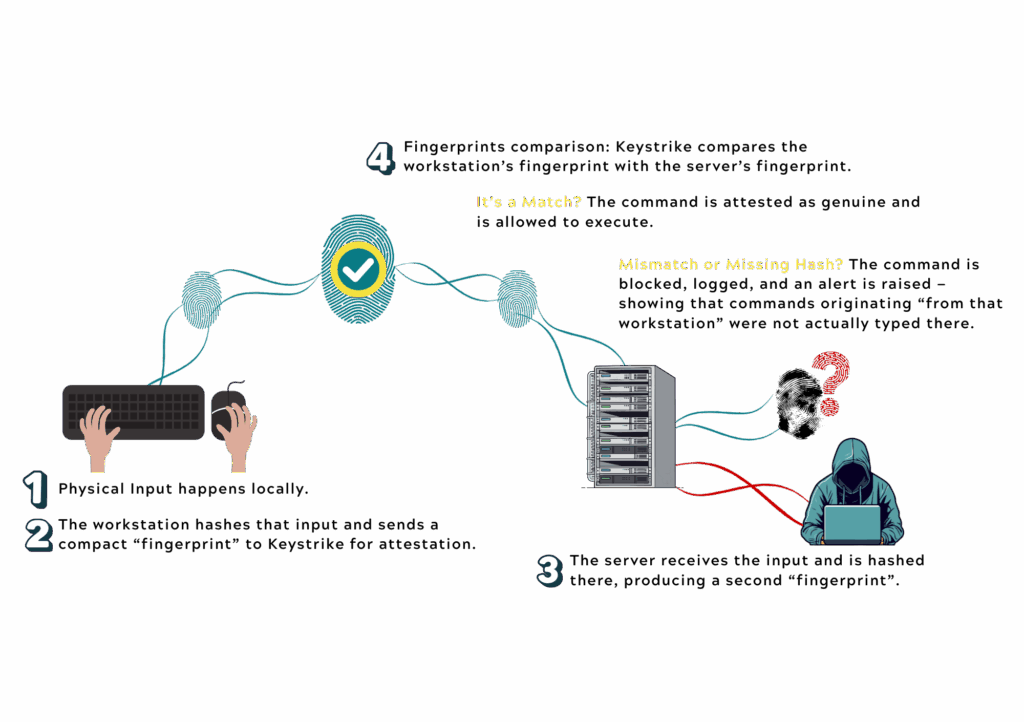
Keystrike validates each command at its source in real time, generating a fingerprint on the user’s workstation and matching it with the command received by the server before it is executed, allowing authentic actions and stopping impersonated ones instantly.
Input Happens Locally
A user physically types a key or clicks on their authorized workstation.
Local Fingerprint Created
The workstation hashes the input, and sends it like a compact fingerprint to Keystrike for attestation.
Server Receives the Input
The same typed input arrives at the server and is encrypted there, producing a second hash or “fingerprint”.
Fingerprints Comparison
Keystrike compares the workstation’s fingerprint with the server’s fingerprint.
Continuous monitoring
This happens for every keystroke and mouse click, continuously, for remote access (SSH, RDP), and cloud/SaaS sessions.
Why it matters?

Stops impersonation
Prevents attackers from injecting commands that didn’t originate from the user’s physical keyboard.

Stops Lateral Movement
Blocks unauthorized commands before they can spread across your network.

True real-time protection
No signatures, no behavior training, no waiting for detection.
Keystrike in few words
- DETECT: Due to the continue attestation, Keystrike immediately detects malicious input.
- PROTECT: The command is blocked, keeping the servers safe.
- REPORT: An alert appears in the Keystrike console and sent instantly to your SIEM tool with zero false positives

Product Demo
Book your personalized demo of Keystrike with Bulwark
Keystrike protects critical systems by verifying that every keystroke and mouse action originates from a trusted, physical device, ensuring commands executed on servers truly come from authorized users, not malware or compromised users.
What can you expect:
- A brief conversation to assess what Keystrike can do to protect your network and devices
- Live product demo with insight into how to get the most out of your partnership with Keystrike
- Discuss your specific use case and goals to determine the best path forward for your business
Schedule a FREE Demo
"*" indicates required fields
